The Internet has become a significant part of our lives. The Internet is just a click away from knowledge, information, communication, from buying a car to buying a pair of socks and many other things. To access the Internet, we need a browser and a search engine, which is how every person uses the Internet, even though only avid internet users know about it.
The Internet isn?t just about using it today, it has harmed individual?s privacy, even personal details, and most importantly, you can use it against one if it comes out in the hands of hackers or fraud. Our data, reserved in a web browser, can be easily unveiled by a simple malware attack, which can be through online purchases, bank information, etc.

The people who hack our data have a very eloquent image on TV, and they very often portray real-life circumstances so that no one can ever pinpoint the true image of the person. Many internet companies and service providers assemble the users? data that contain an enormous amount of information.
There can be personal information also, which is very valuable to the criminals as they can use them for various reasons and works. Many reports sprinkle light on the scams that cybercriminals are doing by addressing the people?s information stored on commonly used browsers.
When these criminals maliciously get people?s information or materials, they try to achieve more and more information, like how people are allocating their time, what online activities they are doing, etc.
There is a kind of digital criminal who can rattle our day-to-day existence after getting information according to our systems? findings. To redeem ourselves from these scams, we all need to educate ourselves on detecting malware and ransomware.
Our lot of information is reserved deep in our browsers like a password entered automatically and saved, phone numbers, location data, etc., which cybercriminals can oppress in numerous ways. Using the person?s history, the cybercriminals evaluate which site or app is frequently used by the person who can also comprise sensitive apps like banking information or online transaction details.
Slowly the attackers bind up the puzzle pieces and begin to come together by obtaining small information about the user.
Here are six browser secrets that only avid internet users know about that might help us to keep data shielded :
1. Know Which Public Wi-fi To Trust
We should be very prudent while traveling as we use public wi-fi, which is less secure than our one because we did not have any idea who has a setup wi-fi and who else is bridging to it. Therefore, we should always connect to the HTTPS server as it is secure rather than HTTP.
2. Disable And Manage Third-Party Permissions
The third-party applications that users download onto their devices have certain permissions turned on without apprising the gadget owner. Managing the setting permissions is crucial to keep our data secure from hackers.
3. Encrypt The Data
To encrypt the data is effortless; while backing up the data in case of any emergency, it is compulsory to encrypt it yourself as an active approach to data protection. Furthermore, if the device has been stolen, it is also possible to encrypt the hard drive so that you can preserve data.
4. Incognito Windows
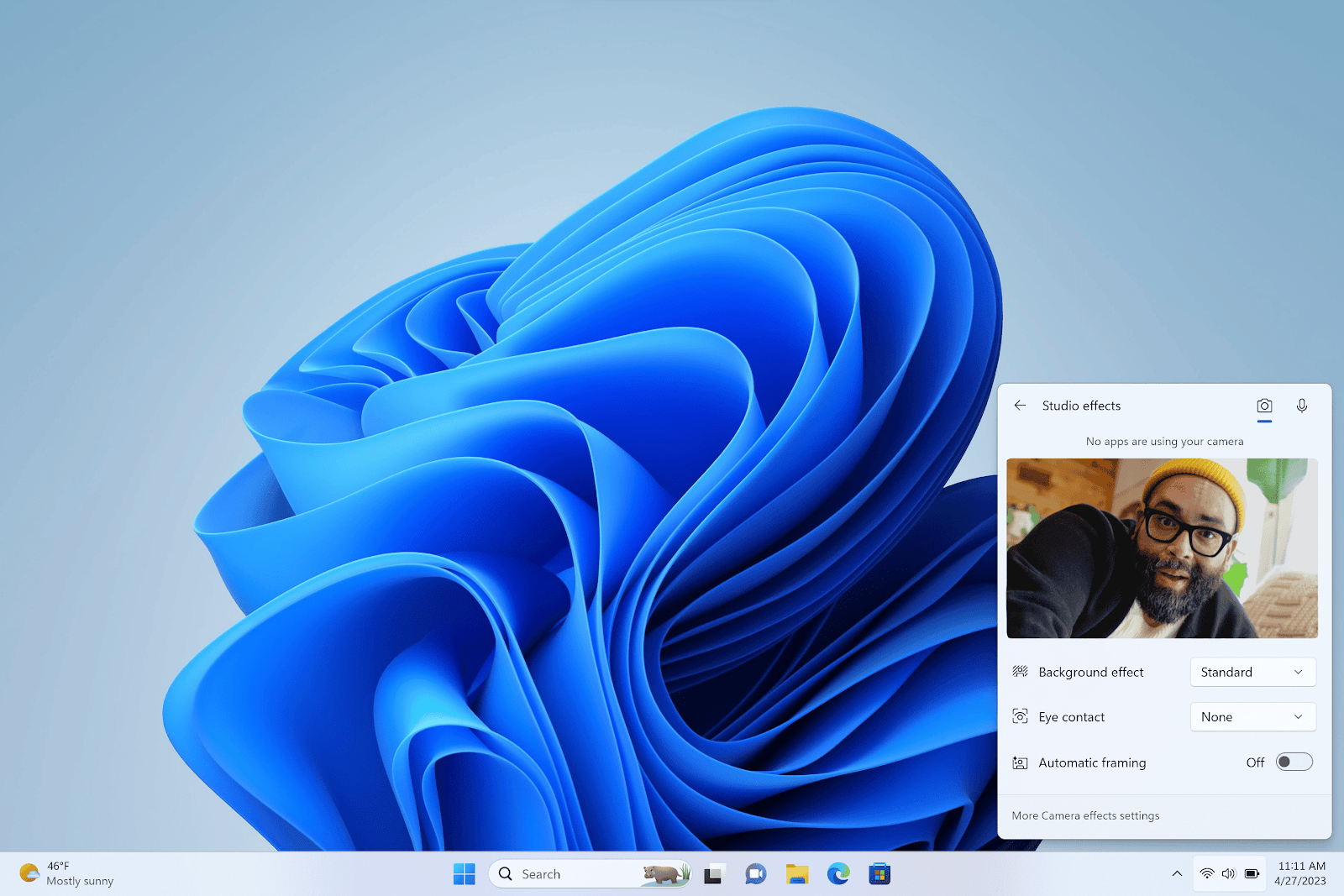
Many people use incognito mode as all the dominant browsers offer incognito mode or private browsing mode, which means that a user?s preceding activity will not be logged and stored in history. With this website, you can do this faster.
5. Mute An Email Thread
you can mute a chain of emails as we do not want to access those emails. The muted email threads can be unmuted whenever we want.
6. Overwrite Any Deleted Files
People thought that once something is deleted, it is elapsed forever, but that?s not the case. So instead, we should overwrite those files that move into our technological trash bin.
Internet privacy can also be known as a subset of data privacy. Internet privacy engages the right or authorization of personal privacy concerning the storing, repurposing, equipping to third parties, and flashes of information about oneself via the Internet.
The users who are regularly online should employ firewalls and anti-malware programs in their systems. For example, if the user is using Safari, he/she can do the following things.
- Close all the tabs at once
- Open recently closed tabs.
- Press-and-hold back and forward buttons to access history
- Reorder tabs
- Close tabs remotely
- Request desktop site
- Find on-page
- Bookmark and reading list
- Bookmark and reading list
When the attacker accesses our systems at a very large level, then he/she may be able to achieve information about a person?s periodic routine like when he started the work, when he/she logs out from work, etc. Some accounts are very wise, which can be targeted easily by criminals through emails.
There are some privacy mechanisms that an individual should take care of and take some precautions to save their accounts or information. People can browse in an incognito mode that grants an internet browsing experience with a less digital footprint, which means nothing will be saved.
We should also eliminate the cookies and debilitate auto-fills. We can also use a VPN, i.e., a virtual private network, to ensure that our internet connection is protected from any prying eyes.
In today?s century, people need to take more provisions and be alert from the online risks as these might not give any proclamations or suspicions. They enter our systems without our knowledge. To be safe, it is essential to make equity between our privacy/security and the technology?s convenience.